Using NGINX as a reverse proxy, with Letsenctypt to generate SSL certificates and secure access to my externally exposed services, was a real game-changer for me, automating something that in the past has been a real challenge. NGINX Proxy Manager simplifies things even further and saves me having to edit multiple nginx.conf files.
I have several services running on my FreeNAS server that are accessible outside of my local network. Way back when, I’d secured most things using self-certified certificates, but when these stopped working with most browsers, a different solution was required. I’ve bought a few certificates in the past, and also tried to maintain Letsencrypt ones manually, although it was always a challenge and I needed a better solution.
I eventually came across the idea of a FreeNAS jail running NGINX and configured as a reverse proxy, which also runs Certbot to generate and automatically renew Letsencryprt certificates. I blogged about it here, so won’t go through it all again now, other than to say it’s worked beautifully for the past few years.
All of my services are accessed from a subdomain from either my personal (personal.com) or work (work.com) domains, so look something like service.personal.com. To set up a new service, I create an A record on my domain Cpanel pointing to my external IP address (which is a static address through my ISP). My router forwards all requests on port 80 (HTTP) and 443 (HTTPS) to this jail, which forces https, validates the certificate and redirects the traffic to the appropriate service.
I could probably have a single nginx.conf file, but it would be quite big, and I’ve just found it easier to have individual ones for each service, so I have several service.conf files in my ./nginx/sites-enabled folder. There’s quite a lot of duplication, but creating a new service can generally be done by simply copying an old one and tweaking the forwarding, certificate and location settings.
I use Certbot to create the SSL certificates from Letsencrypt, and a cronjob runs once a week to check if any are due for renewal, and when there are less than 30 days to the certificate expiry they automatically renew. It works perfectly, and also sends me an e-mail to confirm when they’ve renewed. Everything is manual editing at the command line in the jail, but I’m pretty comfortable with it now, even if my knowledge of NGINX syntax is a little limited. I know enough to make it work, most of the time!
Someone on the iXsystems forum had mentioned NGINX Reverse Proxy as a solution to simplify this, but I was a little apprehensive as I didn’t want to break something that was working so well. Given how critical this is, I decided to test it out spinning up a new VM (ubuntu 20.4 LTS), installing Docker and Docker Compose and then following the pretty simple instructions on the website.
It’s a very clean and simple interface and works incredibly well, so much so, that my old jail is now switched off and everything is now running through this, although the screenshot isn’t of my system 😉
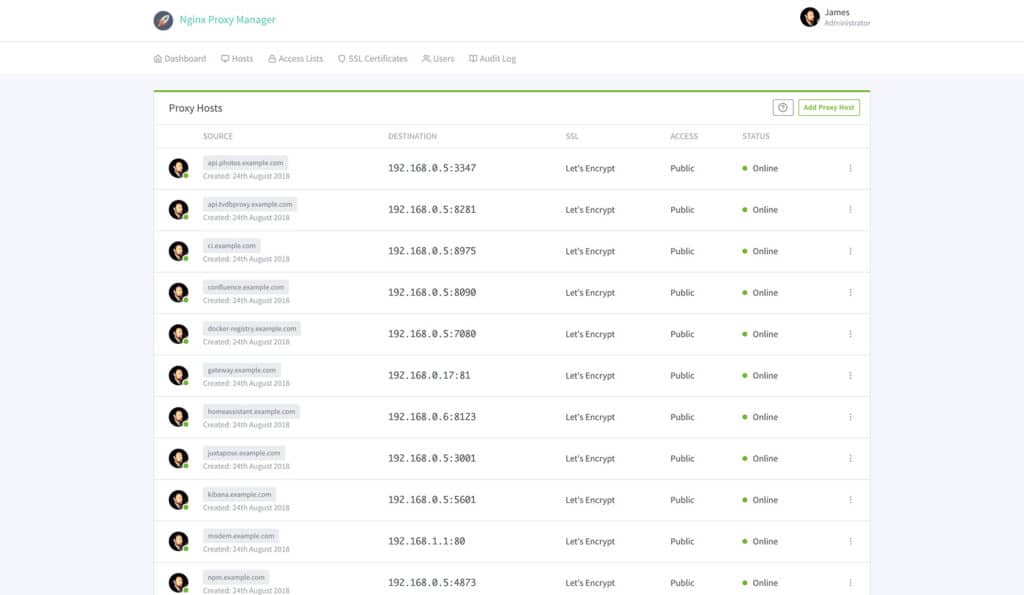
I’m only using it as a reverse proxy, so haven’t even looked at any of the other options. I also haven’t been running it long enough for any of the certificates to renew, but I’m pretty hopeful that they will be given the feedback online They were all recreated within 24 hours, so it will be pretty easy to see if they do and fix within the 30 days if they don’t.
It’s a much nicer solution than the one I was using, even if that did work so well. Not having to SSH into my FreeNAS server and then console into the jail, to edit config files using nano isn’t something I’m going to miss!
If you’ve ever tried to set up an NGINX reverse proxy and failed, this makes the job pretty simple. If you already have one, this makes administering things much more straight forward. NGINX Proxy Manager is worth a look in either situation.

Trackbacks/Pingbacks